Cloud security automation streamlines threat detection and response by automating repetitive tasks like patch management, vulnerability scanning, and access control. By using automated tools, you can quickly identify and mitigate risks, ensuring consistent security policies across dynamic cloud environments. As cloud environments scale, automation helps maintain security compliance, improves visibility, and reduces manual intervention, ultimately lowering operational costs and enhancing overall security posture.
As cloud environments scale and change rapidly, maintaining a strong security posture becomes more complex and resource-intensive. Traditional, manual security processes often fail to keep pace with frequent infrastructure changes.
Nearly 50% of security incidents come from user or permission mismanagement. This is a common risk in dynamic environments where manual oversight is difficult to sustain.
Cloud security automation helps address this challenge by reducing dependence on manual effort. By automating patch management, vulnerability scanning, and incident response, teams close security gaps faster and respond to threats in real time. This also helps maintain consistent security controls as cloud environments continue to change.
In this blog, you’ll learn the 6 essential steps to implement cloud security automation to help you stay ahead of threats while keeping your cloud environments secure and efficient.
What is Cloud Security Automation & Why Does It Matter?
Cloud security automation uses automated systems to detect, assess, and reduce security threats across cloud environments. It manages repetitive activities such as patch management, vulnerability scanning, access control, and incident response.
This approach reduces manual effort in securing complex, dynamic cloud infrastructures while enabling faster and more consistent protection.
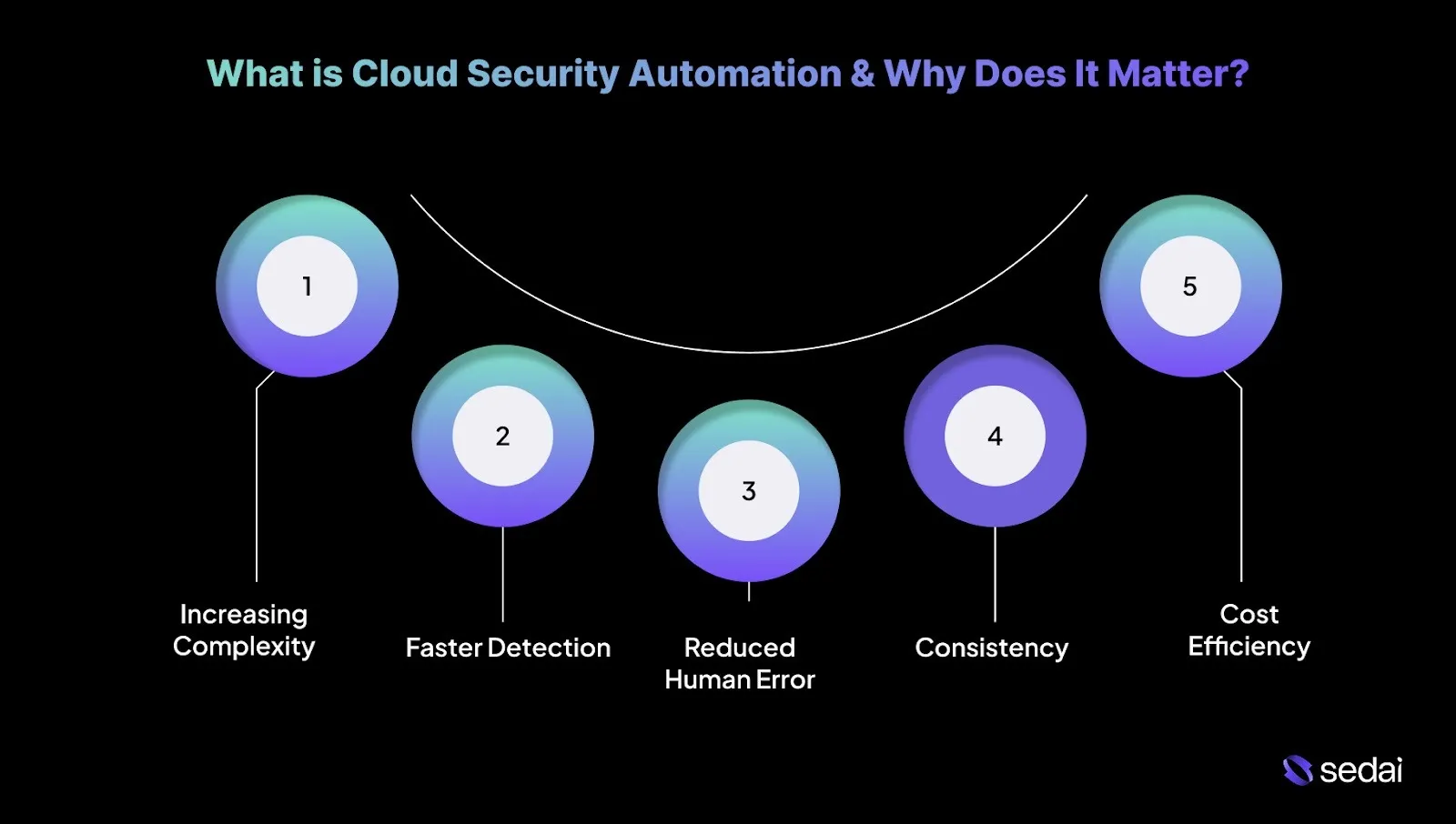
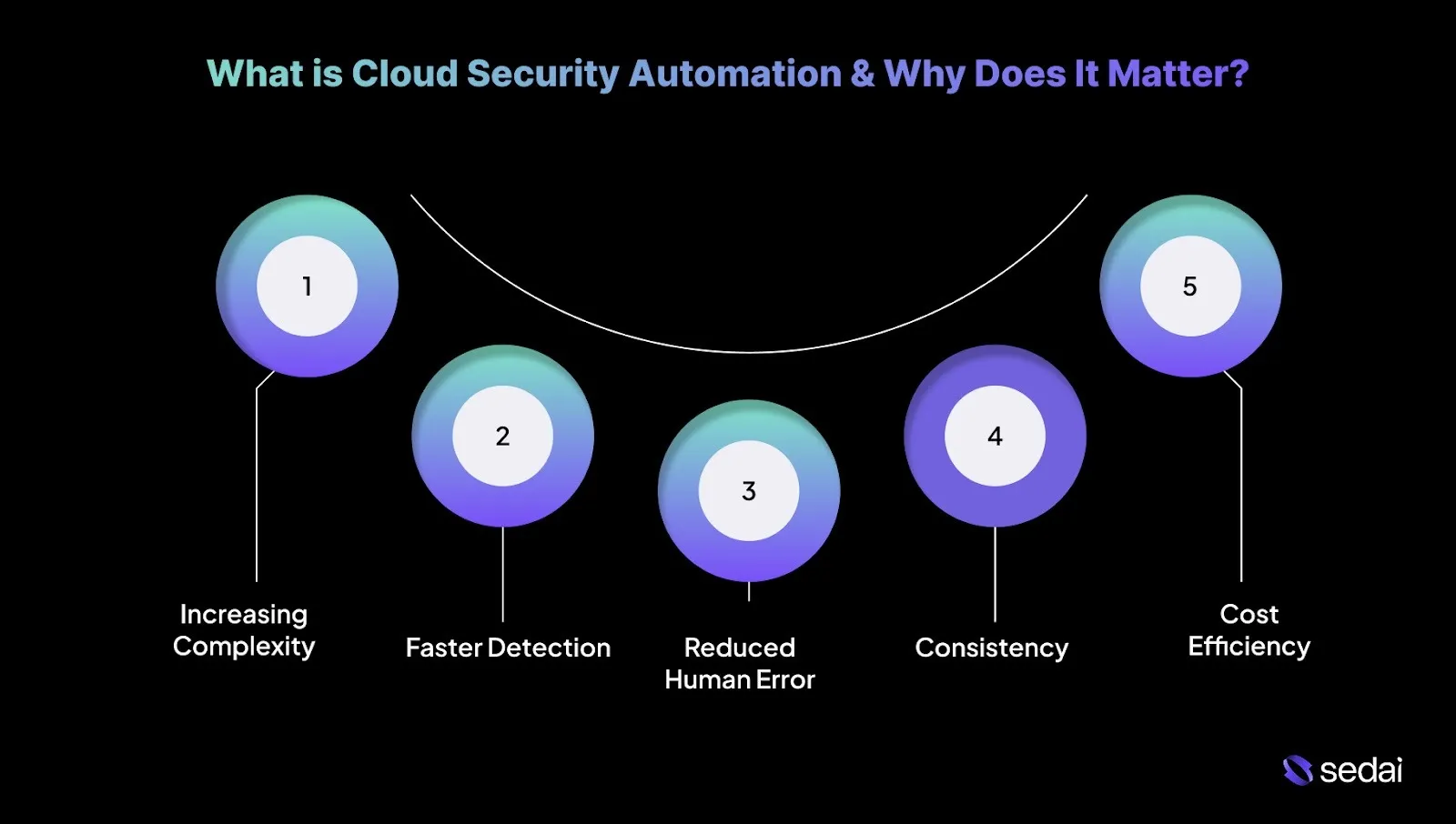
Here’s why cloud security automation matters:
1. Increasing Complexity of Cloud Environments
Cloud environments change continuously, driven by infrastructure updates, dynamic scaling, and frequent deployments.
Security automation helps you handle this complexity by continuously monitoring resources and enforcing security policies without constant manual involvement.
2. Faster Detection and Response
Security events like unauthorized access or data exposure can escalate quickly if not addressed immediately. Automated systems detect threats in real time and initiate predefined responses within seconds, reducing response time and limiting impact.
For example, if an application shows unusual behavior, such as accessing restricted data, automation can isolate the affected resource before the issue spreads.
3. Reduced Human Error
Even experienced engineers can make mistakes, particularly in high-pressure or fast-changing environments. Automation minimizes human error, which remains a common source of security vulnerabilities.
4. Consistency and Compliance
Security and compliance frameworks like GDPR, SOC 2, and PCI-DSS require uniform policy enforcement across all cloud resources.
Automation ensures security controls are applied consistently at scale, regardless of environment size or complexity. It also simplifies audits by maintaining detailed logs and clear evidence of compliance activities.
5. Cost Efficiency
By automating routine security tasks, teams can focus on higher-impact work such as threat analysis and incident investigation.
Reducing manual effort for tasks such as firewall updates or vulnerability scans lowers operational overhead and makes security management more cost-effective overall.
Once you understand what cloud security automation is and why it matters, the benefits it brings to everyday security operations become much clearer.
Suggested Read: What is Cloud Automation? A Complete Guide
Benefits of Cloud Security Automation
Cloud security automation provides clear advantages for engineers responsible for complex cloud environments. Here’s how cloud security automation directly benefits you:
1. Faster and Smarter Decision-Making
Automation allows security systems to prioritize risks and act in real time based on predefined conditions. When a potential breach is detected, the system can immediately escalate or reduce the issue according to severity, without waiting for manual review.
2. Smooth Integration with DevOps Pipelines
Cloud security automation integrates smoothly with CI/CD pipelines, embedding security checks and vulnerability scans at every stage of development.
Automating security early in the delivery cycle helps identify issues before they reach production, improving both development velocity and security outcomes.
3. Adaptive to Emerging Threats
As cloud environments evolve, threat patterns change as well. Automated security systems adapt by learning from historical data, threat intelligence feeds, and past incidents.
This enables continuous refinement of security policies without constant manual tuning, helping teams stay aligned with emerging risks.
4. Improved Visibility Across Cloud Infrastructure
Automated tools deliver continuous, real-time visibility across the cloud environment. You can track infrastructure changes, monitor access patterns, and detect unusual activity across platforms.
This level of visibility supports faster identification and response to potential security issues.
5. Enhanced Collaboration Between Teams
By reducing the burden of repetitive security tasks, automation allows engineers to focus on higher-value work. This encourages closer collaboration between security, operations, and DevOps teams, supporting shared ownership of cloud security and more effective decision-making.
6. Optimized Resource Allocation
Security automation scales protections in line with infrastructure demand. During traffic spikes or security events, automated systems can allocate additional resources to security functions, such as expanding monitoring capacity or adjusting firewall controls.
Once you understand the benefits of cloud security automation, the next step is to identify the practical actions needed to implement it effectively.
Also Read: Understanding and Setting Up Auto Remediation
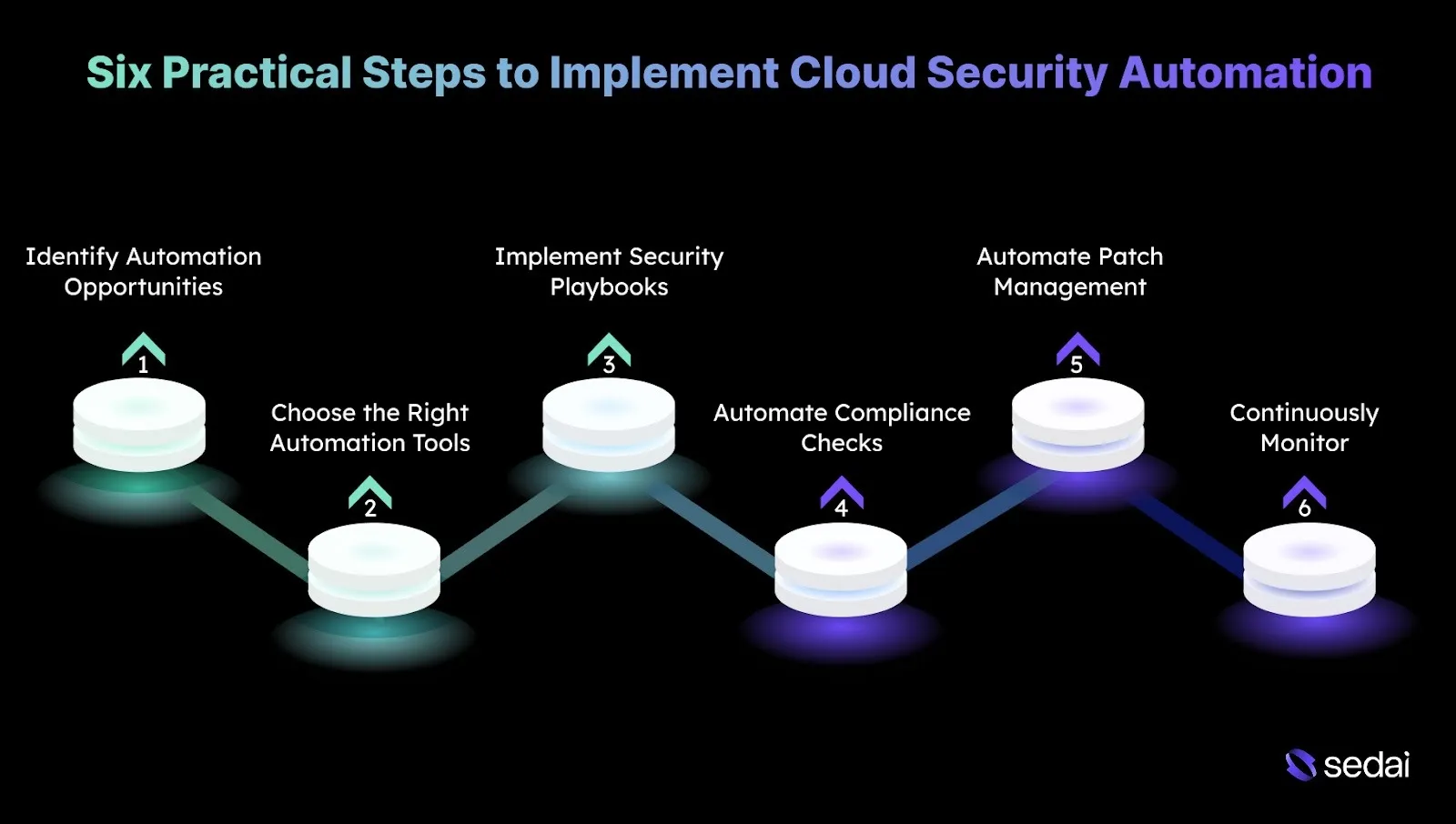
Six Practical Steps to Implement Cloud Security Automation
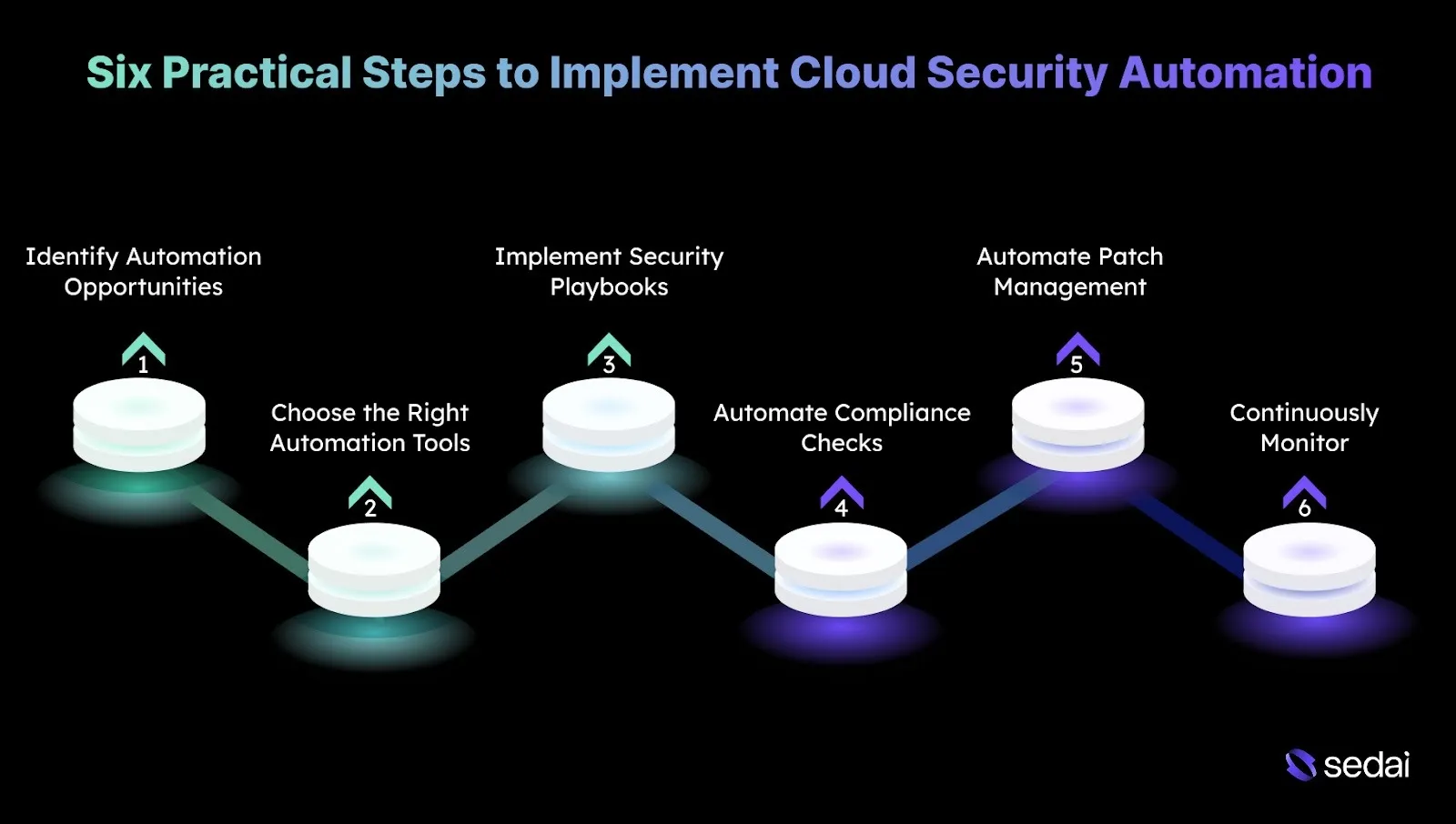
Implementing cloud security automation requires deliberate planning and disciplined execution to ensure security tasks are automated without reducing effectiveness.
Here are the following six steps to implement cloud security automation in a controlled and reliable way:
1. Assess Your Current Security Posture and Identify Automation Opportunities
Start with a detailed assessment of your existing cloud security setup. Identify repetitive, manual tasks that consume engineering time, such as patching, vulnerability scanning, access provisioning, or compliance checks.
Prioritize areas where automation can deliver quick value without introducing risk, such as fastening incident response or enforcing consistent security policies across environments.
Tip: Map each repetitive task to potential automation, considering its blast radius and prioritizing high-impact areas where errors would be costly.
2. Choose the Right Automation Tools and Integrate with Cloud Platforms
Select automation tools that align closely with your cloud providers, whether AWS, Azure, or Google Cloud, and support your specific security requirements. Ensure these tools integrate cleanly with existing workflows and DevOps pipelines to avoid operational friction.
Tip: Evaluate tools for features and for their ability to provide observability into automated actions for audit and troubleshooting.
3. Define and Implement Security Playbooks for Incident Response
Create automated incident response playbooks that execute predefined actions when specific security events occur. For example, if an instance shows abnormal behavior, the playbook can automatically isolate the resource, revoke credentials, and alert the SOC team.
Tip: Simulate playbook execution in a staging environment to validate both safety and speed before applying it in production.
4. Automate Compliance Checks and Reporting
Automate compliance validation and reporting to maintain continuous alignment with regulatory requirements such as GDPR, SOC 2, and HIPAA.
Use cloud-native services like AWS Config or Azure Policy to continuously evaluate configurations and flag violations. Automated reporting simplifies audits and reduces the manual effort required to track compliance controls.
Tip: Align automated compliance checks with tagging and resource metadata to enable granular, team-level accountability and actionable reporting.
5. Automate Patch Management and Vulnerability Scanning
Implement automated vulnerability scanning across cloud resources, including VMs, containers, and databases, and pair it with automated patch management.
Tools like AWS Inspector, Azure Security Center, or third-party platforms can continuously scan for known vulnerabilities. Automated patching policies ensure critical updates are applied promptly, minimizing exposure while avoiding manual processes.
Tip: Prioritize patching and scanning based on exposure and asset criticality, rather than scanning everything equally, to optimize risk mitigation and operational efficiency.
6. Continuously Monitor and Fine-Tune Automation Rules
Continuously monitor the effectiveness of automated security controls and refine rules as threats evolve. Review outcomes regularly to ensure automation behaves as expected.
Machine learning-driven services can help identify emerging threat patterns. Use these insights to adjust automation workflows so they remain aligned with current risk profiles and security intelligence.
Tip: Establish a feedback loop that correlates automated actions with incident outcomes, refining rules to reduce false positives and missed threats over time.
After learning how to implement cloud security automation, it’s important to be aware of the common challenges teams may face along the way.
Common Challenges With Cloud Security Automation
While cloud security automation delivers clear benefits, it also introduces challenges that you need to account for to avoid operational risks. Understanding these issues upfront helps ensure automation strengthens security rather than creating new gaps.
Below are some common challenges to consider with effective solutions.
Must Read: Best Cloud Storage Providers in 2025: What You Need to Know
How Sedai Supports Cloud Security Automation?
Many cloud environments still depend on manual processes and static configurations, which struggle to keep pace as workloads scale and risk profiles change. Without automation, teams often spend more time managing infrastructure than focusing on proactive security initiatives.
Sedai is an autonomous cloud optimization platform that continuously manages resource allocation across compute, storage, and networking based on real workload behavior.
By keeping cloud infrastructure efficient and predictable, Sedai indirectly strengthens security automation efforts. It helps limit configuration drift, reduce resource sprawl, and maintain consistent runtime states.
What Sedai Offers:
1. Autonomous Resource Optimization
Sedai continuously evaluates real workload behavior and optimizes compute, storage, and networking resources. It helps reduce cloud costs by up to 50%. This reduces the need for frequent manual configuration changes that often introduce security risks.
2. Real-Time Rightsizing
Instance sizes and memory allocations are adjusted based on live usage data, preventing over-sized or underutilized resources that can complicate visibility and security monitoring.
3. Continuous Monitoring and Adjustment
Machine learning–driven monitoring keeps environments aligned with performance targets, reducing operational noise that can divert attention from security-critical tasks.
4. Automatic Efficiency Remediation
When inefficiencies or performance bottlenecks arise, Sedai can automatically address them. This lowers operational backlog and allows security teams to focus on threat detection, response, and compliance. It saves up to 6x the engineering effort required for manual fixes.
5. Holistic Optimization
Sedai operates across compute, storage, and networking layers, helping maintain consistent configurations that support standardized security baselines.
6. Multi-Cloud and Multi-Platform Support
Support for AWS, Azure, and Google Cloud enables unified resource management across environments, reducing complexity in multi-cloud security operations.
7. SLO-Driven Decisions
Optimization actions are aligned with application Service Level Objectives (SLOs), ensuring performance goals are met while freeing your teams to advance dedicated security automation initiatives.
Final Thoughts
Cloud security automation plays a critical role in maintaining a strong, efficient, and scalable security posture across cloud environments. As security tasks increase in volume and complexity, automation ensures policies are enforced consistently, and threats are detected and addressed in real time.
This is why engineering teams increasingly depend on automation to simplify security operations. Through continuous monitoring, response, and adaptation, platforms like Sedai simplify cloud management by automating resource optimization and reducing operational overhead that often pulls focus away from critical security work.
Through continuous resource and performance adjustments, Sedai enables teams to prioritize high-impact initiatives such as strengthening security while maintaining efficiency and alignment without manual effort.
Start using automation today to create a more responsive and secure cloud environment.
FAQs
Q1. How can I ensure that automated security responses don’t disrupt business operations?
A1. To avoid disruptions, use a tiered automation approach where high-impact actions require manual review or approval. Define clear incident response playbooks that map actions to severity levels, and always validate automated workflows in staging or non-production environments before rolling them out broadly.
Q2. How do I manage cloud security automation in multi-cloud environments?
A2. Multi-cloud setups benefit from centralized security platforms that support multiple providers. Tools enable unified automation for threat detection, compliance monitoring, and policy enforcement across AWS, Azure, and Google Cloud.
Q3. Can cloud security automation be integrated with traditional on-premises security tools?
A3. Yes, many cloud security automation platforms integrate with on-premises tools through APIs or hybrid deployment models. This allows consistent security controls, visibility, and incident response across both cloud and on-prem environments.
Q4. How often should I update automated security rules to stay aligned with new threats?
A4. Security rules should be reviewed and updated regularly, typically quarterly or after major security incidents. Machine learning-based tools can further support this by automatically adapting rules as new threat intelligence and patterns emerge.
Q5. What role does machine learning play in cloud security automation?
A5. Machine learning enables cloud security automation to analyze historical and real-time data, identify anomalous behavior, and predict potential threats. Over time, it improves detection accuracy, reduces false positives, and helps refine security policies with minimal manual effort.